
Hackers hijacking Instagram accounts of companies and influencers, demanding ransom

Hackers are hijacking the Instagram accounts of companies and influencers with huge followings in a new phishing campaign identified by Secureworks.
The cybersecurity company said it discovered the effort in October, finding hackers taking over prominent accounts and demanding a ransom.
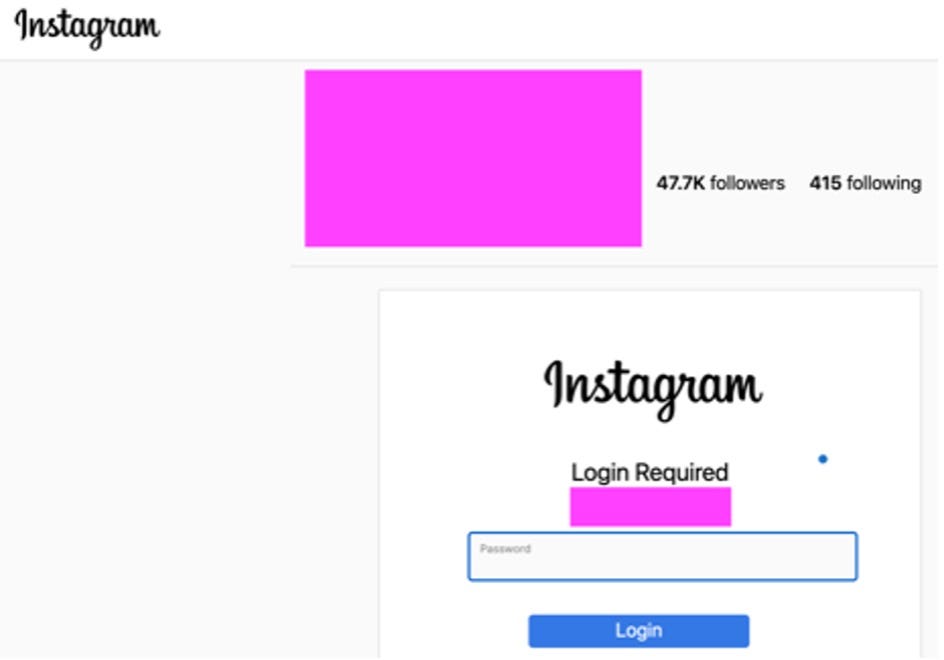
The people behind the attack start by sending a message pretending to be Instagram, notifying Instagram users of a purported instance of copyright infringement. There is a link in the message that takes victims to a website controlled by the hackers. From there, the user is asked to enter their Instagram login information, giving the attackers full access to their accounts.
“After gaining control of the Instagram account, the threat actors change the password and username. The modified username is a variation of ‘pharabenfarway’ followed by a number that appears to be the number of followers for the hijacked account,” Secureworks explained.
“The threat actors add a comment to the profile that ‘this Instagram account is held to be sold back to its owner.’ The comment includes a link composed of a shortened WhatsApp domain (wa . me) and a contact number. Clicking the link opens a WhatsApp chat conversation prompt with the threat actors. The threat actors also contact the victim via text message at the phone number listed on the account and start negotiating a ransom in exchange for access to the account.”
Secureworks said that based on domain creation dates, it believes the hackers hijacked a number of accounts and began the campaign in 2021.
Through searches on underground forums, Secureworks found a post from September where someone tied to the hackers is selling access to hijacked Instagram accounts for about $40,000.
According to Secureworks, the hackers offer phone numbers indicating they are based in Russia and Turkey. Other evidence indicates at least one of the attackers is based in Turkey.
“In one incident, threat actor communications originated from a Turkish-language version of Instagram. Additionally, the page source of one of the phishing websites references the Turkish hizliresim . com file-sharing service. The infrastructure associated with this campaign is based in Turkey and other countries,” Secureworks said.
The company noted that attacks like this could also give hackers access to email accounts or other corporate resources if passwords were reused.
Source: https://www.zdnet.com/article/hackers-hijacking-instagram-accounts-of-companies-and-influencers-demanding-ransom/#ftag=RSSbaffb68


















