
Malware campaign uses clever ‘captcha’ to bypass browser warning

A malware campaign uses a clever captcha prompt to trick users into bypassing browsers warnings to download the Gozi (aka Ursnif) banking trojan.
Yesterday, security researcher MalwareHunterTeam shared a suspicious URL with BleepingComputer that downloads a file when attempting to watch an embedded YouTube video about a New Jersey women’s prison.
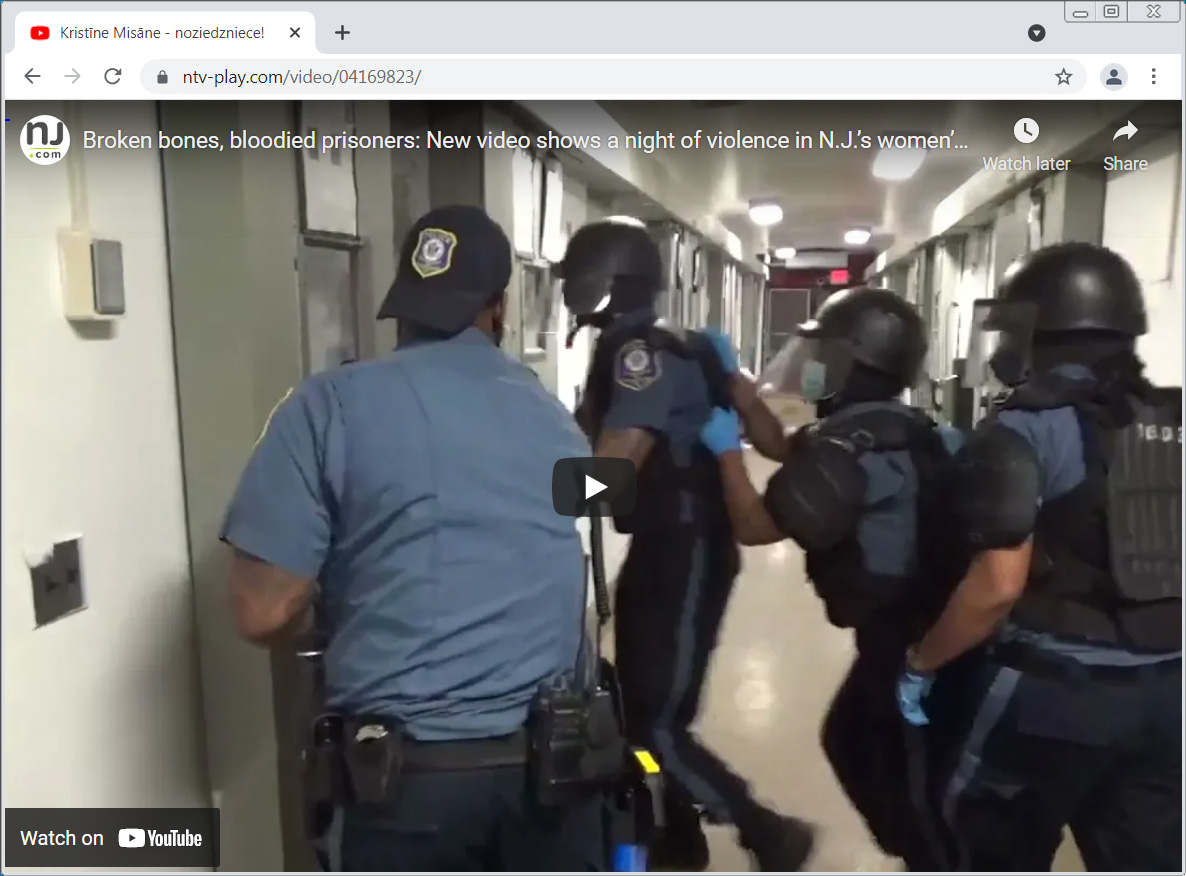
Source: BleepingComputer
When you click on the play button, the browser will download a file named console-play.exe [VirusTotal], and the site will display a fake reCaptcha image on the screen.
As this file is an executable, Google Chrome automatically warns that the file may be malicious and prompts whether you wish to ‘Keep’ or ‘Discard’ the file.
To bypass this warning, the threat actors are displaying a fake reCaptcha image that prompts the user to press the B, S, Tab, A, F, and the Enter buttons on their keyboard, as shown below.
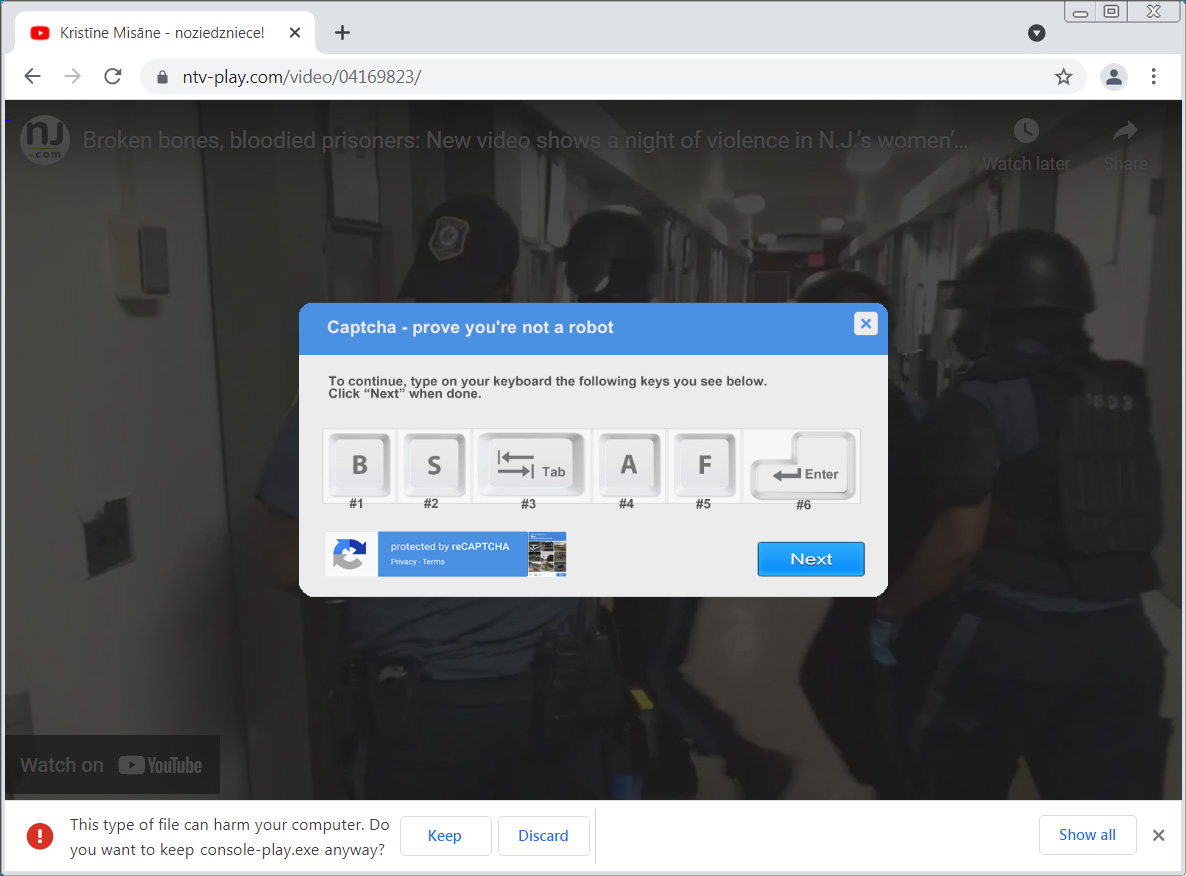
Source: BleepingComputer
While pressing the B, S, A, and F keys do not do anything, pressing the Tab key will make the ‘Keep’ button become focused, and then pressing the ‘Enter’ key will act as a click on the button, causing the browser to download and save the file to the computer.
As you can see, this fake captcha prompt is a clever way to trick a user into downloading a malicious file that the browser is warning could be malicious.
After a certain amount of time, the video will automatically play, potentially making users think the successful ‘captcha’ allowed it.
Site distributes Ursnif information-stealing trojan
If a user runs the executable, it will create a folder under %AppData%Bouncy for .NET Helper and install numerous files. All of these files are a decoy, other than the BouncyDotNet.exe executable, which is launched.
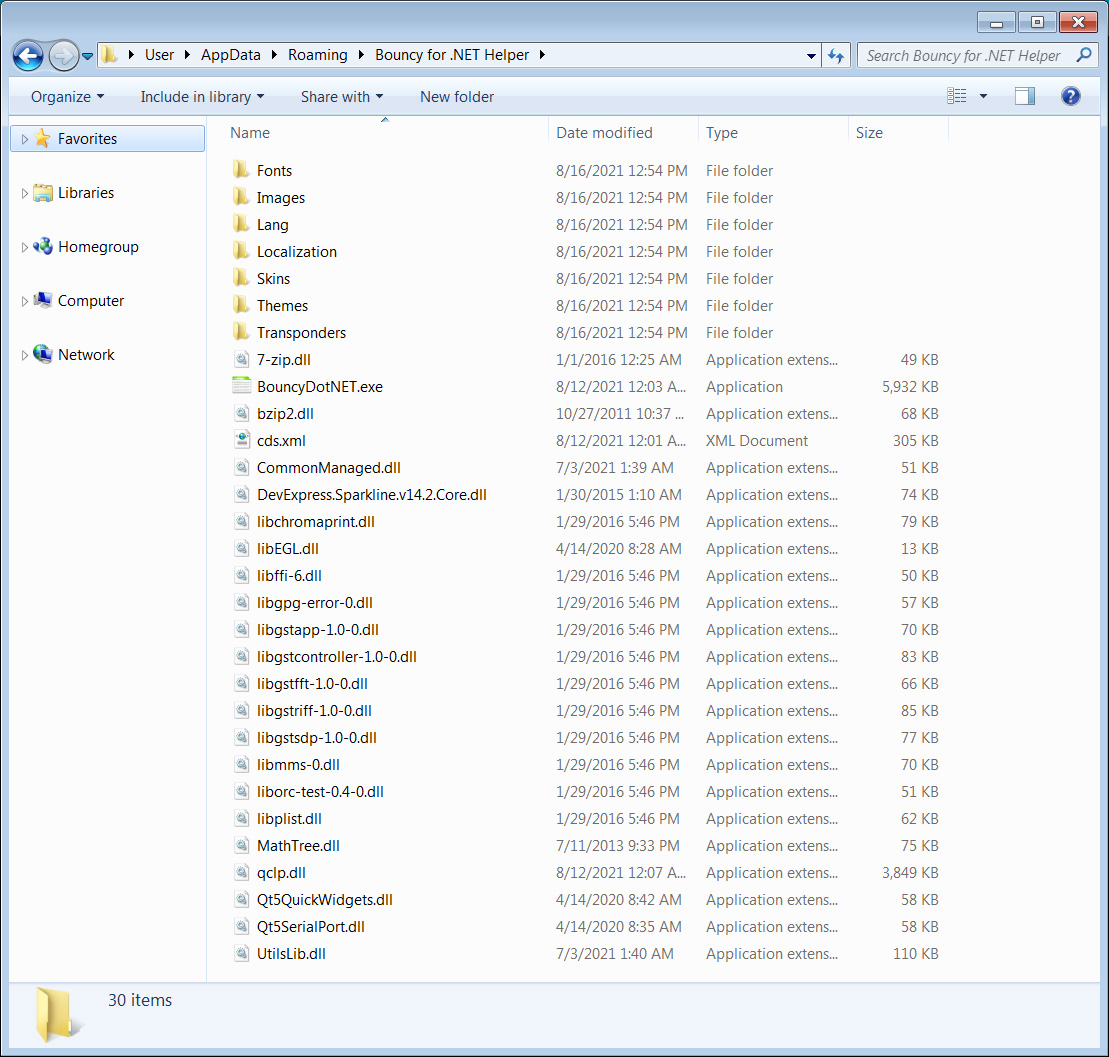
Source: BleepingComputer
While running, BouncyDotNet.exe will read various strings from the Windows Registry used to launch PowerShell commands.
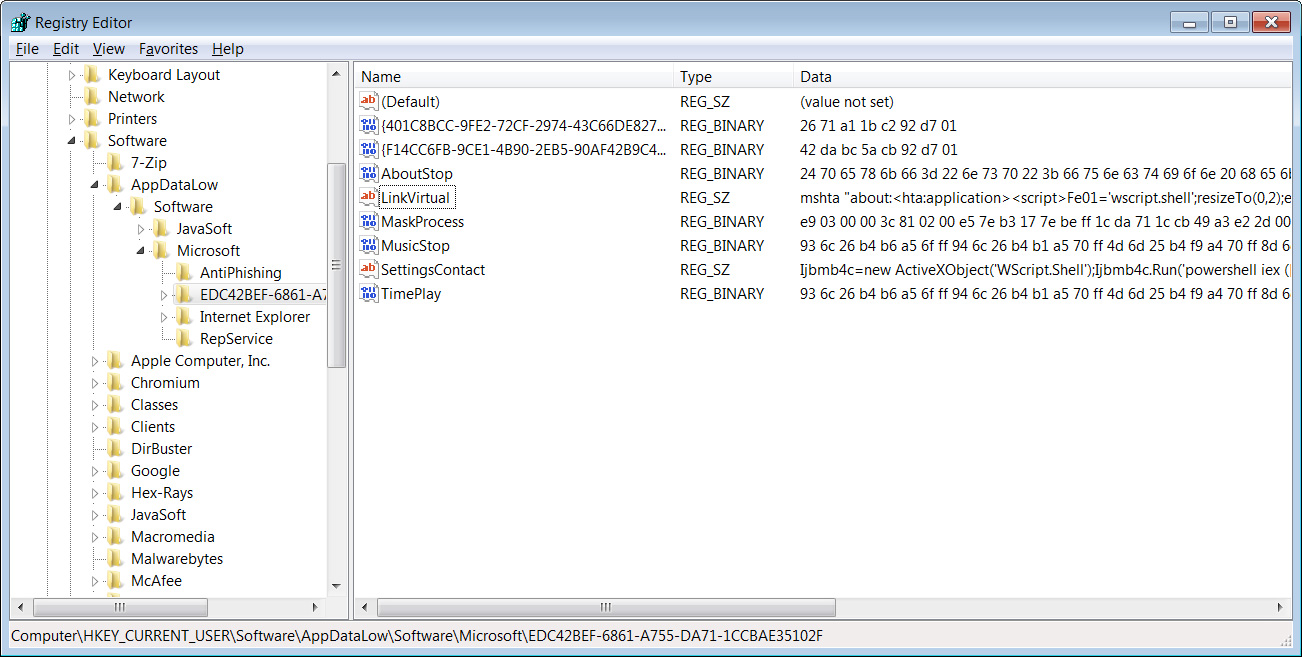
Source: BleepingComputer
These PowerShell commands will compile a .NET application using the built-in CSC.exe compiler that launches a DLL for the Ursnif banking trojan.
Once running, Gozi will steal account credentials, download further malware to the computer, and execute commands issued remotely by the threat actors.
If you are infected with Ursnif, you should immediately change the passwords for your online accounts.
Source: https://www.bleepingcomputer.com/news/security/malware-campaign-uses-clever-captcha-to-bypass-browser-warning/


















