
Microsoft pushes emergency update for Windows PrintNightmare zero-day


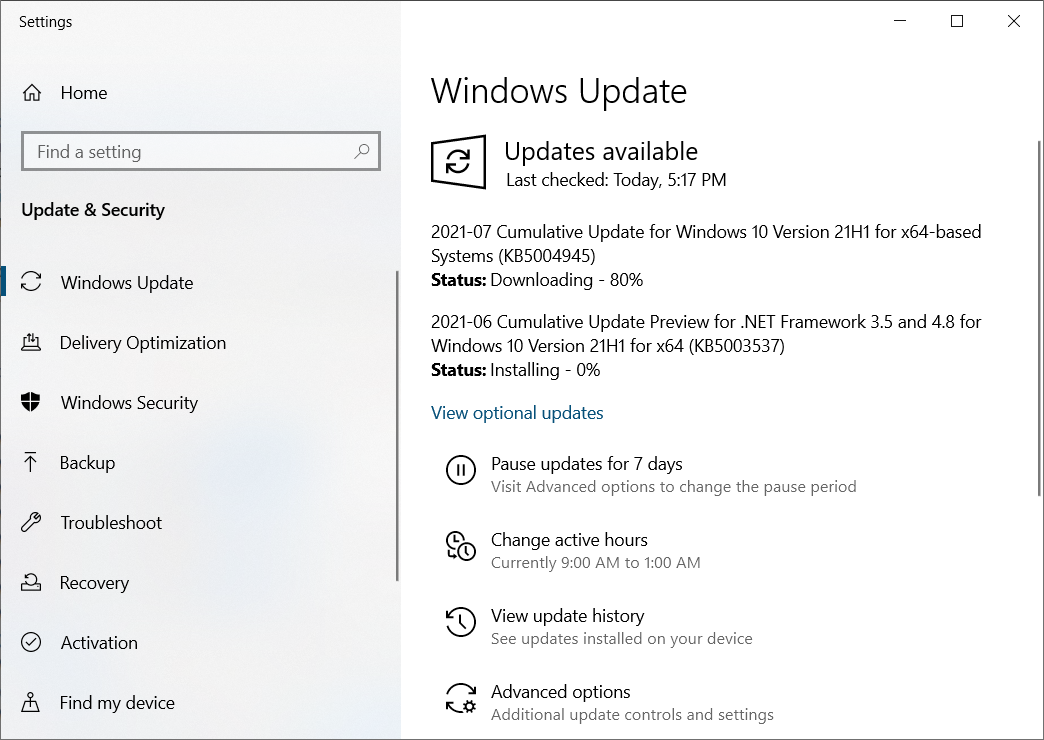
Microsoft has released the KB5004945 emergency security update to address the actively exploited PrintNightmare zero-day vulnerability in the Windows Print Spooler service and impacting all supported Windows versions.
The remote code execution bug (tracked as CVE-2021-34527) allows attackers to take over affected servers via remote code execution (RCE) with SYSTEM privileges, as it will enable them to install programs, view, change, or delete data, and create new accounts with full user rights.
Detailed instructions on how to install these out-of-band security updates for your operating system, are available in the support documents linked below:
- Windows 10, version 21H1 (KB5004945)
- Windows 10, version 20H1 (KB5004945)
- Windows 10, version 2004 (KB5004945)
- Windows 10, version 1909 (KB5004946)
- Windows 10, version 1809 and Windows Server 2019 (KB5004947)
- Windows 10, version 1803 (KB5004949)
- Windows 10, version 1507 (KB5004950)
- Windows 8.1 and Windows Server 2012 (Monthly Rollup KB5004954 / Security only KB5004958)
- Windows 7 SP1 and Windows Server 2008 R2 SP1 (Monthly Rollup KB5004953 / Security only KB5004951)
- Windows Server 2008 SP2 (Monthly Rollup KB5004955 / Security only KB5004959)
Security updates have not yet been released for Windows 10 version 1607, Windows Server 2016, or Windows Server 2012, but they will also be released soon, according to Microsoft.
“Release notes associated with these updates might publish with a delay of up to an hour after the updates are available for download,” Microsoft said.
“Updates for the remaining affected supported versions of Windows will be released in the coming days.”
Mitigation also available
Microsoft urges customers to install these out-of-band security updates immediately to address the PrintNightmare vulnerability.
Those who cannot install these updates as soon as possible should check out the FAQ and Workaround sections in the CVE-2021-34527 security advisory for info on how to protect their systems from attacks exploiting this vulnerability.
The available mitigation options include disabling the Print Spooler service to remove printing capability locally and remotely or disabling inbound remote printing through Group Policy to remove remote attack vector by blocking inbound remote printing operations.
In the second case, Microsoft says that “the system will no longer function as a print server, but local printing to a directly attached device will still be possible.”
CISA has also published a notification on the PrintNightmare zero-day last week encouraging admins to disable the Windows Print Spooler service on servers not used for printing.
Source: https://www.bleepingcomputer.com/news/security/microsoft-pushes-emergency-update-for-windows-printnightmare-zero-day/


















