Windows 11 makes TPM Diagnostics tool its first optional feature

Windows 11 comes with a new optional feature called ‘TPM Diagnostics’ that allows administrators to query the data stored on a device’s TPM security processor.
When it comes to Windows 11, Microsoft is placing all its bets on the TPM 2.0 security processor as a requirement for the OS to power some of its security features.
“PCs of the future need this modern hardware root-of-trust to help protect from both common and sophisticated attacks like ransomware and more sophisticated attacks from nation-states. Requiring the TPM 2.0 elevates the standard for hardware security by requiring that built-in root-of-trust,” explains Microsoft in a new blog post.
“TPM 2.0 is a critical building block for providing security with Windows Hello and BitLocker to help customers better protect their identities and data. In addition, for many enterprise customers, TPMs help facilitate Zero Trust security by providing a secure element for attesting to the health of devices.”
A TPM is a hardware security processor that is used to securely “protect encryption keys, user credentials, and other sensitive data behind a hardware barrier so that malware and attackers can’t access or tamper with that data.”
While this sounds like an important device, many users with older computers that run Windows 10 perfectly are upset as they are now being forced into purchasing new hardware if they want to upgrade to Windows 11.
While Microsoft has received considerable pushback due to this new requirement, a new optional feature shows how serious they are about TPM security processors and their use on Windows 11.
Windows 11 includes a new TPM Diagnostics tool
Microsoft’s investment in the use of TPM processors shows in a brand new Windows 11 command-line tool called “TPM Diagnostics” that allows administrators to query a TPM for stored information.
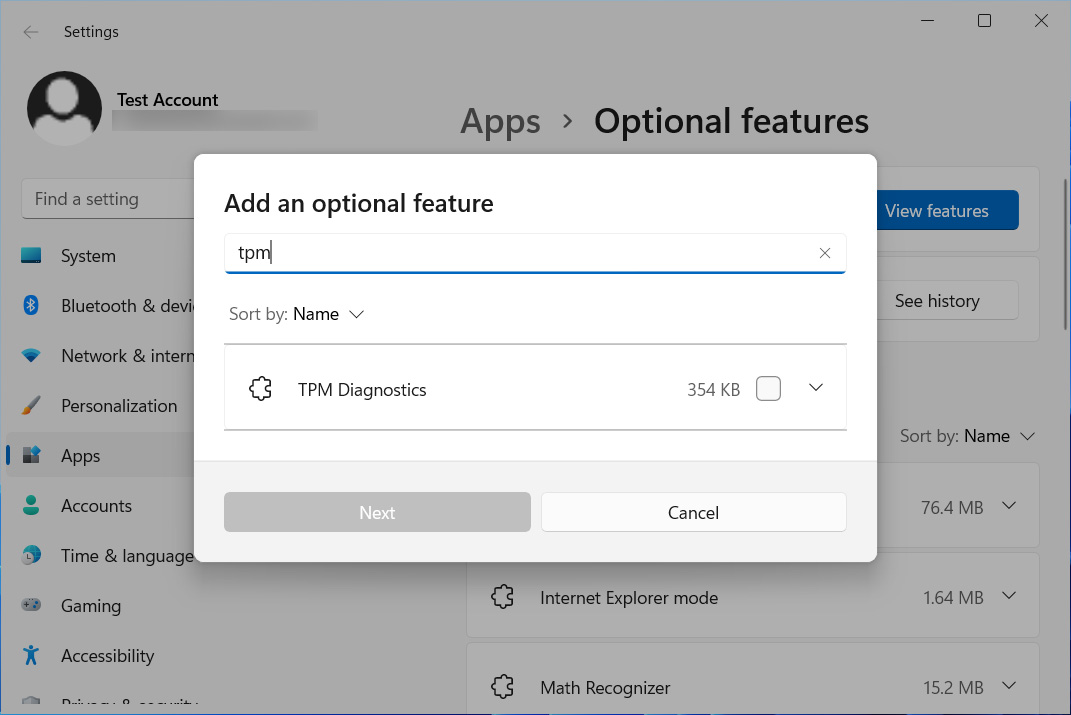
When installed, there will be a new ‘tpmdiagnostics.exe’ executable located in the C:WindowsSystem32 folder that allows you to query various information from your installed TPM.
While Microsoft already includes a Trusted Platform Module Management console (tpm.msc), it only provides a small amount of information and the ability to clear the TPM.
The TPmDiagnostics.exe tool allows access to much more significant information, including Windows Attestation Identity Keys, Endorsement Key certificates, others keys stored in the TPM, boot counters, information about what tasks are running, information about the TPM, and much more.
As I only have Windows 11 install in a virtual machine which does not have TPM capabilities, I tested the program by copying the files to a Windows 10 box that has a TPM 2.0 module installed.
The TpmDiagnostics.exe program only appears to be available to Windows 10 Pro users and should be run from an Elevated Command Prompt, and when executed by itself will list a help file of available commands.
For example, the command TpmDiagnostics.exe GetCapabilities will list the capabilities and settings of the installed TPM processor, as shown below.
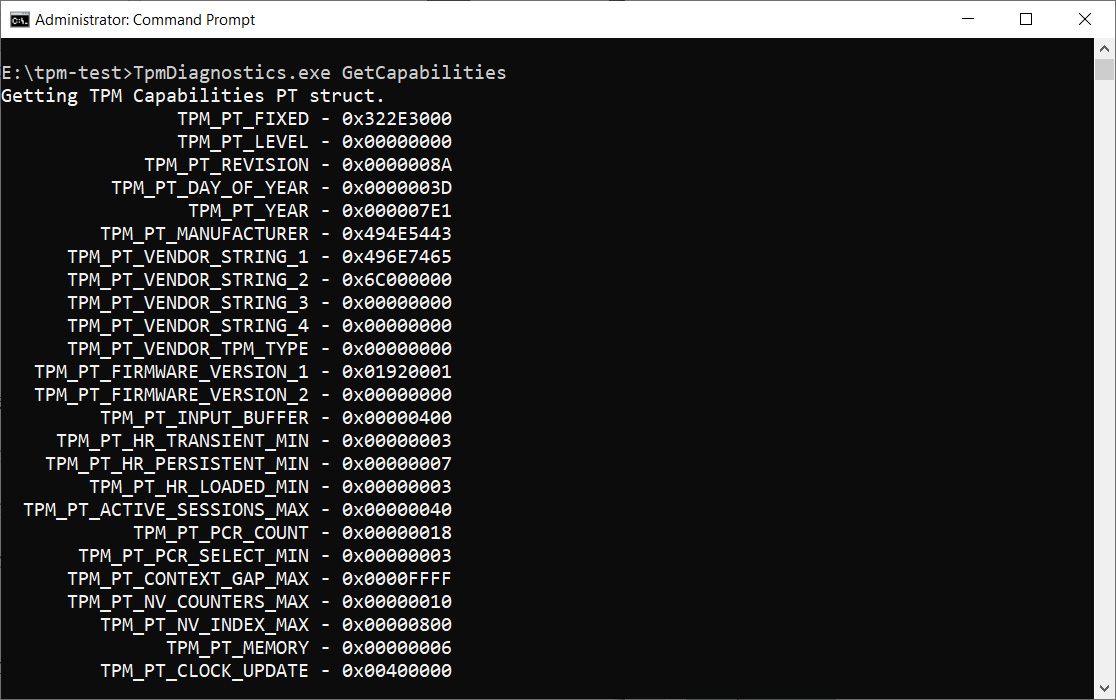
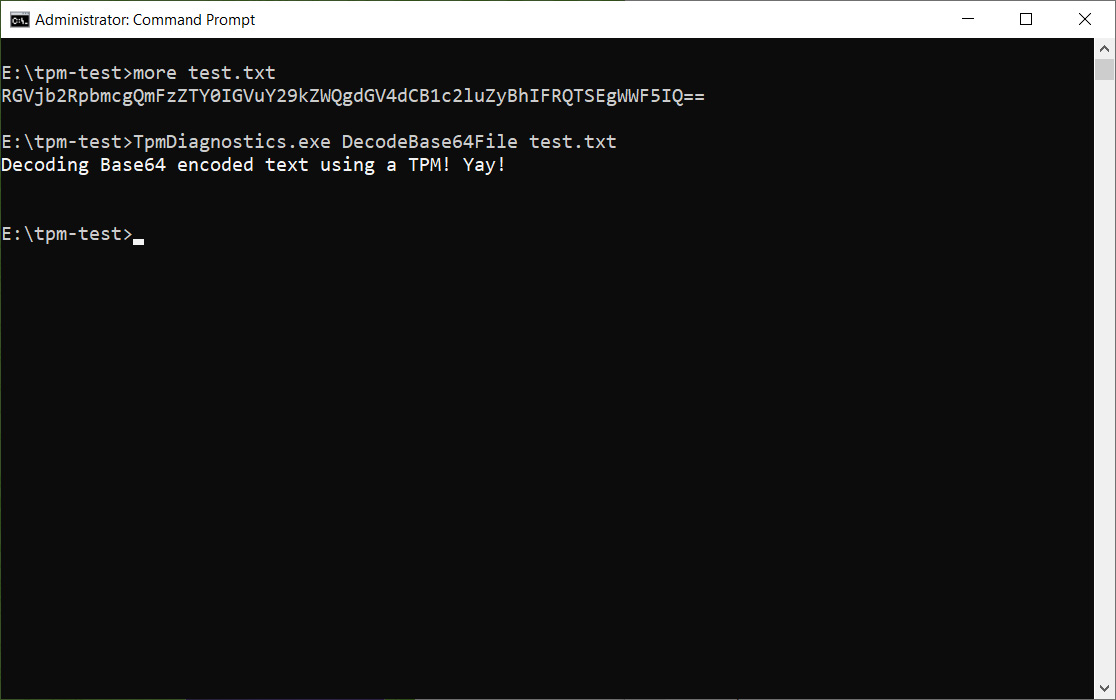
In addition to querying stored keys and other information, you can also use the TPM to perform encoding/decoding of Base64, Hexadecimal, and Binary files.
Unless you understand what data is being stored in your TPM, I don’t advise messing with it too much to avoid accidentally removing the keys necessary for the operation of your device.
However, the Microsoft Trusted Platform (TPM) documentation and the new TpmDiagnostics.exe tool can provide a wealth of information about the underlying security mechanics of Windows 11.
The complete list of commands available in the tpmdiagnostics.exe tool are:
tpmdiagnostics : A tool for Windows 10 build 22000 Copyright (c) Microsoft Corporation. All rights reserved. Flags: PrintHelp ( /h -h ) PromptOnExit ( -x /x ) UseECC ( -ecc /ecc ) UseAes256 ( -aes256 /aes256 ) QuietPrint ( -q /q ) PrintVerbosely ( -v /v ) Use the 'help' command to get more information about a command. Commands: TpmInfo: GetLockoutInfo IsOwned PlatformType CheckFIPS ReadClock GetDeviceInformation IfxRsaKeygenVulnerability GatherLogs [full directory path] PssPadding IsReadyInformation TpmTask: MaintenanceTaskStatus ShowTaskStatus IsEULAAccepted ProvisionTpm [force clear] [allow PPI prompt] TpmProvisioning: PrepareTPM CanUseLockoutPolicyClear CanClearByPolicy AutoProvisioning: IsAutoProvisioningEnabled EnableAutoProvisioning DisableAutoProvisioning [-o] EK: EkInfo ekchain EkCertStoreRegistry GetEkCertFromWeb [-ecc] [cert file] GetEkCertFromNVR [-ecc] [cert file] GetEkCertFromReg [-ecc] [ output file ] GetEk [-ecc] [key file] CheckEkCertState InstallEkCertFromWeb InstallEkCertFromNVR InstallEkCertThroughCoreProv EKCertificateURL WindowsAIK: InstallWindowsAIK [-skipCert] WinAikPersistedInTpm UninstallWindowsAIKCert GetWindowsAIKCert [cert file] IsWindowsAIKInstalledInNCrypt EnrollWindowsAIKCert GetWindowsAIKPlatformClaim ["fresh"] [output file] OtherKeys: PrintPublicInfo [ srk / aik / ek / handle ] [-asBcryptBlob / -RsaKeyBitsOnly / -RsaSymKeyBitsOnly] [-ecc] TestParms [ SYMCIPHER | RSA ] [ algorithm specific arguments ] EnumerateKeys NVStorage: EnumNVIndexes DefineIndex [index] [size] [attribute flags] UndefineIndex [index] ReadNVIndexPublic [index] WriteNVIndex [index] [data in hex format | -file filename] ReadNVIndex [index] NVSummary NVBootCounter: CheckBootCounter ReadBootCounter [/f] PCRs: PrintPcrs PhysicalPresence: GetPPTransition GetPPVersionInfo GetPPResponse GetPPRequest TPMCommandsAndResponses: CommandCode [hex command code] ResponseCode [hex response code] Tracing: EnableDriverTracing DisableDriverTracing FormatTrace [etl file] [output json file] DRTM: DescribeMle [MLE Binary File] Misc: Help [command name] DecodeBase64File [file to decode from base 64] EncodeToBase64File [file to encode] ReadFileAsHex [file to read] ConvertBinToHex [file to read] [file to write to] ConvertHexToBin [file to read] [file to write to] Hash [hex bytes or raw value to hash] GetCapabilities Source: https://www.bleepingcomputer.com/news/security/windows-11-makes-tpm-diagnostics-tool-its-first-optional-feature/